How to Patch/Upgrade Java (JDK and JRE) in both Oracle Home and OEM Agent 13.5 home to latest certified version
A vulnerability scan from the customer pointed out many problems due to old patch backups and old JDK versions installed in a Oracle VM.
Many of the problems were with the files:
/u01/app/oracle/product/oem13c/agent/agent_13.5.0.0.0/oracle_common/jdk/jre/lib/rt.jar
/u01/app/oracle/product/19.0.0/dbhome_1/jdk/jre/lib/rt.jarWhat I learned:
- OEM Agent 13.5 default java version is 1.8.0_261, also after patching to the latest RU!
- Oracle OPatch has its own JRE and this is not updated when applying latest JDK patch for Oracle Home
- Upgrade JDK in Oracle Home is online
What I already knew:
- Oracle DB Release Updates (RU) install the before-last JDK version.
- There is in CPU4 – Oracle Critical Patch Update (CPU) Jan 2026 for Oracle Database Products (or the document for last CPU) a specific Patch to upgrade the JDK to the latest certified version (online patch).
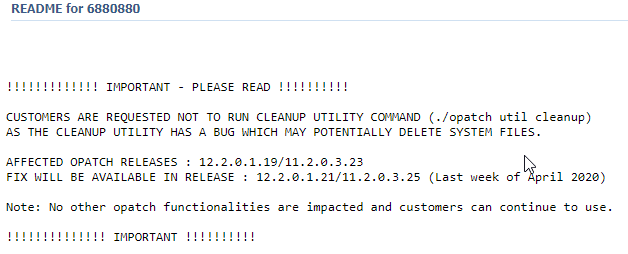
- The old patches are kept in a folder “.patch_storage”, for the needs of rollback. Vulnerability tools are picky and find it as potentially dangerous. The latest OPatch versions have a “util obfuscate” which will change the name and a little the contents of the files, so vulnerability tools do not find it. I blogged about it two years ago: Opatch now obfuscates its own backups – the new “opatch util Obfuscate” option explained
Below how I “cleanup” the vulnerabilities at my customer VM. This instructions are for java version 1.8.0_481, latest certified for Oracle in January 2026 :
(more…)